Benford’s Law as a Security Perimeter | AI Governance
Before a single neuron fires, your system should subject incoming data to a "Physics Check."
Benford’s Law is the ultimate sub-millisecond filter for detecting synthetic tampering, manual data entry fraud, and bot-driven injection.
1. The Mathematical "Tell"
Benford’s Law (the Law of First Digits) isn't just a statistical curiosity; it is a signature of natural data. In any naturally occurring dataset—transaction amounts, population sizes, or sensor readings—the leading digit '1' appears ~30.1% of the time, while '9' appears less than 5% of the time.
The Governance Insight: Fraudsters and automated bots are notoriously bad at mimicking this distribution. When they invent numbers (e.g., to bypass a credit limit or trigger a specific model response), they tend to distribute digits uniformly. A simple frequency check reveals the "fingerprint" of human or synthetic intervention before the data ever reaches your model.
2. The "Defense-in-Depth" Flow
By placing Benford’s Law at the perimeter, you move from a "Model-Only" architecture to a Deterministic Gate architecture. This creates a sub-millisecond perimeter that catches bulk fraud before your models even start "thinking."
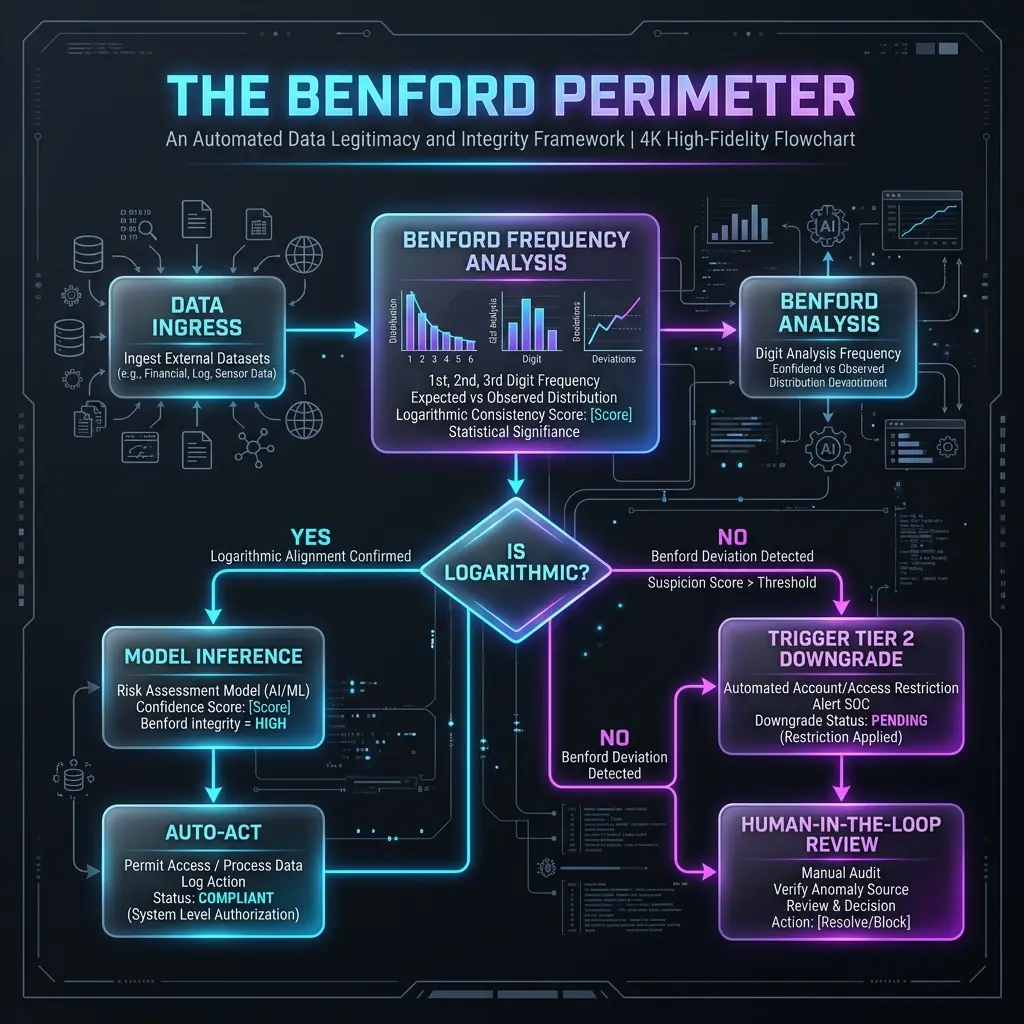
The Perimeter Flowchart Logic:
- Ingestion: Raw numerical data enters the system.
- The Benford Gate (Deterministic):
- Check: Does the leading digit frequency match the logarithmic curve?
- Latency: < 1ms.
- Tiered Response:
- Pass: Data proceeds to the Probabilistic Model (Tier 4 Autonomy).
- Flag: Data is immediately downgraded to Tier 2 (Advise). The AI suggests a fraud score, but a human must approve the action.
- Audit Trail: The Benford "Z-score" is logged as part of the Causal Trace, providing immediate evidence for the 4-minute root cause diagnosis.
3. Strategic Advantage: Slashing the "Cost of Proof"
Running a large-scale fraud model (like a Random Forest or a LLM-based agent) on every single packet is expensive in terms of both compute and latency.
| Approach | Logic | Cost (per 1k packets) |
|---|---|---|
| Traditional | Run 1,000 packets through a $0.05 model | $50.00 |
| Architecture of Proof | Run 1,000 through $0.0001 Benford Gate; drop 5% anomalies; run 950 through model | ~$47.51 |
This is how you turn a "Cost Center" (Compliance) into a "Value Center" (Efficiency).
4. The Benford Threshold: When to Downgrade Autonomy
In a high-velocity environment, you cannot stop every minor statistical fluctuation. You need a Deterministic Governor that automates the transition between Control Tiers based on hard evidence.
| Z-Score | Confidence | Governance Action | Logic |
|---|---|---|---|
| < 1.96 | High | Tier 4 (Full Autonomy) | Data is "Natural." The AI model acts without human intervention. |
| 1.96 - 3.0 | Caution | Tier 3 (Act & Notify) | Data is "Suspicious." The AI acts, but an incident report is generated instantly. |
| > 3.0 | Critical | Tier 2 (Advise) | Automated Kill-Switch. The AI is stripped of autonomy; human sign-off required. |
Implementation Sidebar: The "Red Flag" Distribution
When designing your dashboard, look for the "Uniformity Spike." If your leading digits 1 through 9 all hover around 11%, you aren't looking at natural data; you are looking at a "Flat Distribution" attack.
Summary for the C-Suite: "In the Architecture of Proof, we don't trust the model to tell us if the data is real. We trust the physics of the data to tell us if the model should even be running. That is the essence of Deterministic Governance."
Download the Architecture of Proof Checklist
Ready to implement? Get the definitive checklist for building verifiable AI systems.